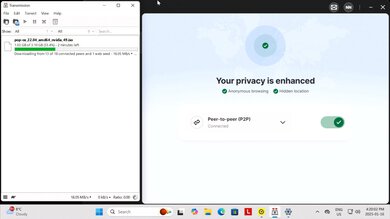
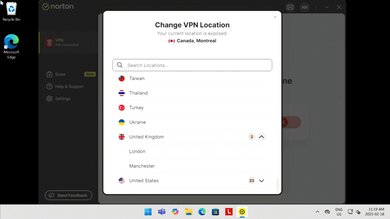
Norton VPN is a service offered by Norton, a US-based company owned by Gen Digital. It's a fairly straightforward service without a particularly comprehensive feature set, but it still has the basics like P2P (torrent) support, geolocation switching, and no data limits.
It's available as part of the Norton 360 security suite or as a standalone service. For more details, see the Differences Between Variants section.
Our Verdict
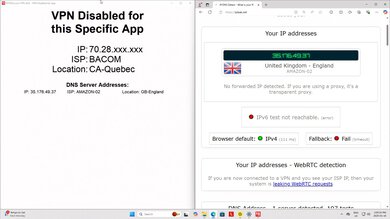
Norton VPN is good for torrenting. It has acceptable security that keeps your IP address and DNS queries hidden while you use it. That said, the kill switch doesn't function properly, as it allows you to reconnect to the internet outside the VPN tunnel after a system reboot or a loss of internet. It has no registration options that preserve your anonymity, as you must provide an email address and password to create an account and use a personally identifiable payment method. Fortunately, it has no data limits and allows you to download torrents.
Proper TLS implementation doesn't leave you vulnerable to man-in-the-middle attacks.
Doesn't leak your IP address or DNS queries.
No registration options that preserve anonymity.
Kill switch doesn't function reliably.
Norton VPN is a disappointing service for private browsing. While its policies contend the company doesn't retain any user traffic, the service does retain other information about your device's hardware and usage information from the VPN client. Norton's parent company has a long history of controversies and legal actions that also make it difficult to trust. Technically speaking, the VPN effectively keeps your IP address and internet traffic hidden, but the kill switch doesn't work effectively, leaking some of your traffic in the case of a software crash.
Doesn't leak your IP address or DNS queries.
No registration options that preserve anonymity.
Parent company has a long history of controversies.
Company collects and retains hardware and application data.
Norton VPN has poor policies and business practices. While it has a no-logging policy that's been verified by independent security audits, its privacy policy indicates that the company collects and retains other application and hardware data from your device. Additionally, its parent company has a long history of controversy and legal actions, making it difficult to place full trust in.
Parent company has a long history of controversies.
Company collects and retains hardware and application data.
Norton VPN has acceptable security. It doesn't leak your IP address or DNS queries while you're connected to it, and it has proper TLS implementation, protecting you from man-in-the-middle attacks. Unfortunately, its kill switch doesn't work as intended, as it leaks some unencrypted traffic upon rebooting your system and after a software crash. This is a concern if you need all your traffic to be encrypted after a system crash.
Proper TLS implementation doesn't leave you vulnerable to man-in-the-middle attacks.
Doesn't leak your IP address or DNS queries.
Kill switch doesn't function reliably.
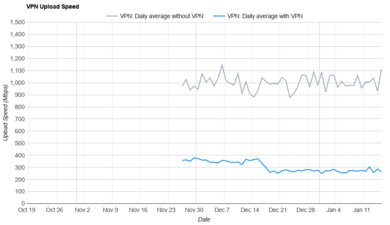
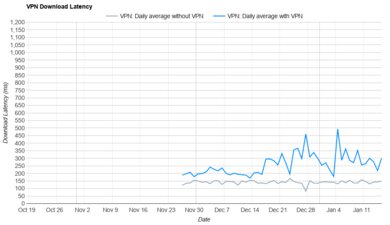
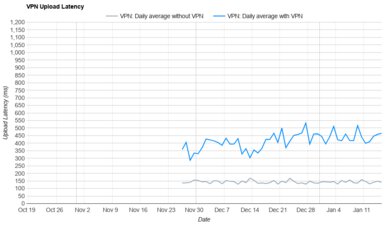
We're testing this VPN's speed on an ongoing basis and will update this verdict when we have more data. See the Performance section of the review to look at the data we've collected so far.
Performance Usages
Changelog
-
Updated Mar 02, 2026:
We've added text throughout the review to correspond with the new privacy tests in Test Bench 0.10.
-
Updated Jan 23, 2026:
We've updated the text throughout the review to reflect the changes from test bench 0.10.1.
- Updated Jan 23, 2026: We've updated this review to Test Bench 0.10.1! This is a minor update to how we conduct our speed tests. Read the changelog for more info.
- Updated Jan 15, 2026: We've updated our review to Test Bench 0.10! This update focuses on privacy and evaluates the trustworthiness of a VPN in keeping your personal information private. Read the changelog for more details.
Check Price
Differences Between Sizes And Variants
Norton VPN offers three different plans that come bundled with additional features. We bought and tested the standard plan.
| Plan | Maximum Devices | Antivirus | Password Manager | Cloud Storage | Parental Controls | Dark Web Monitoring |
|---|---|---|---|---|---|---|
| Standard | 5 | No | No | No | No | No |
| Plus | 5 | Yes | Yes | 10GB | No | Yes |
| Ultimate | 10 | Yes | Yes | 50GB | Yes | Yes |
Note that Norton Secure VPN also comes bundled in some tiers of the Norton 360 security suite.
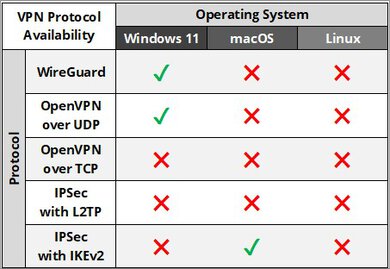
Popular VPN Comparisons
Norton VPN offers middle-of-the-pack performance compared to other VPNs on the market. While it keeps your IP address and DNS queries hidden while you're connected to it, its kill switch doesn't work properly. That means if your computer restarts or your internet connection drops, unencrypted traffic can leak, exposing your IP address. Also, it doesn't have additional features like multi-hop and lacks feature parity across platforms, so your experience will differ significantly depending on which device you use. On top of that, Norton's privacy policy indicates they collect more data from you than many competing services, and its parent company, Gen Digital, has a history of controversies and legal actions that make the service difficult to trust.
To see which services we recommend, check out our articles on the best VPNs, best VPNs for Windows PCs, or the best VPNs for privacy.
Test Results

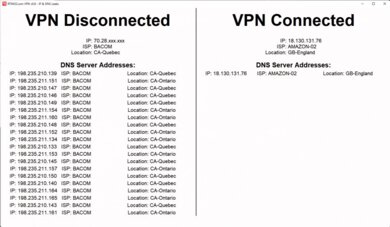
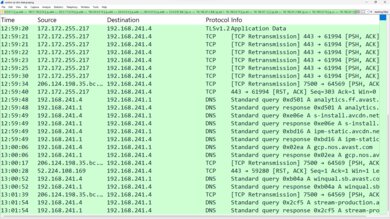
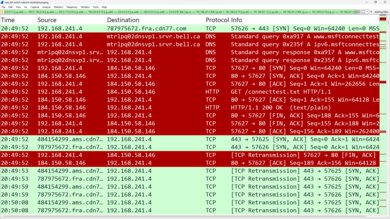
The kill switch doesn't work as intended, as network traffic leaks outside the VPN tunnel after a loss of internet connection and a system reboot. This is a concern if you need to keep all of your traffic encrypted at all times.

Like most VPN services, Norton Ultra VPN doesn't implement BGP properly on all its servers.
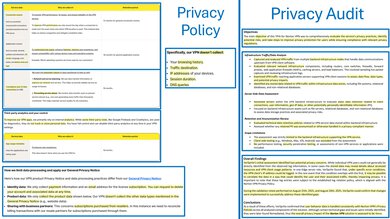
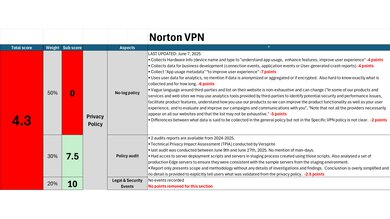
While Norton VPN claims not to log your internet traffic, its privacy policy indicates that the company does collect and retain connection events, application events, hardware information, and app usage metadata. It's not specified whether this data is anonymized or how it's otherwise stored. Norton has, however, published independent audits that confirm the company handles user data in accordance with its policies.
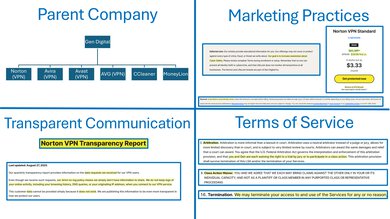
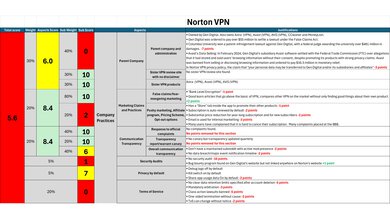
Norton is owned by Gen Digital (formerly Symantec Corporation and NortonLifeLock Inc.), a cybersecurity company that has existed in different forms since 1982. The company has a long history of controversies and lawsuits, ranging from data breaches to patent infringement. There are several other cybersecurity companies in Gen Digital's portfolio that offer VPN services, including Avira, Avast, and AVG, and Noton's privacy policy indicates that your personal data can be transferred to any subsidiary within the corporate umbrella.
Norton hasn't published any independent audits of its security infrastructure, but Gen Digital does offer a bug bounty program. The VPN's terms of service heavily favor the company, mandating arbitration, banning class action lawsuits, allowing the company to terminate accounts without cause, and can change without notice.
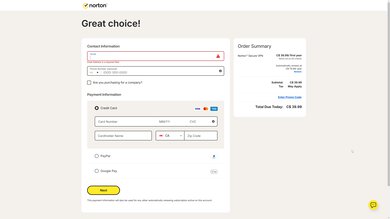
Users online have occasionally reported payment processing issues. We also experienced an issue where Norton's site couldn't process our credit card payment. We had to call customer support and have our payment information processed manually by the agent. Overall, this process was long, cumbersome, and decidedly not private since we had to share de-anonymizing personal information.
You can pay with a credit card, PayPal, or Google Pay.
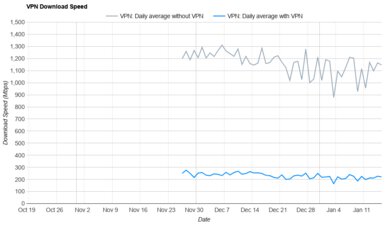
We're testing this VPN's performance on an ongoing basis, and will update the text for the download speed, upload speed, and latency tests when we have more data.
This VPN offers mobile apps for iOS and Android.
Mimic is a proprietary, closed-source protocol that obfuscates traffic by masking itself as an HTTPS connection. Norton advertises that it doesn't require additional configuration, uses less power, resists quantum attacks, and establishes connections quickly. We didn't test this protocol, but other reviews online have found that it has security vulnerabilities.
Norton VPN's ultimate plan includes an advertised maximum of 10 devices.
This VPN has a setting that advertises the ability to access local devices while connected to it, but we weren't able to access anything on a different subnet on our local network, even with the setting enabled.